
Downloads:
1,899
Downloads of v 1.5.7:
694
Last Update:
20 Mar 2021
Package Maintainer(s):
Software Author(s):
- Vadims Podāns
Tags:
sslverifier ssl certificate verifier wpf tool- Software Specific:
- Software Site
- Software Source
- Software License
- Software Issues
- Package Specific:
- Package Source
- Package outdated?
- Package broken?
- Contact Maintainers
- Contact Site Admins
- Software Vendor?
- Report Abuse
- Download
SSL Certificate Verifier
- 1
- 2
- 3
1.5.7 | Updated: 20 Mar 2021
- Software Specific:
- Software Site
- Software Source
- Software License
- Software Issues
- Package Specific:
- Package Source
- Package outdated?
- Package broken?
- Contact Maintainers
- Contact Site Admins
- Software Vendor?
- Report Abuse
- Download
Downloads:
1,899
Downloads of v 1.5.7:
694
Maintainer(s):
Software Author(s):
- Vadims Podāns
SSL Certificate Verifier 1.5.7
- 1
- 2
- 3
All Checks are Passing
3 Passing Tests
Deployment Method: Individual Install, Upgrade, & Uninstall
To install SSL Certificate Verifier, run the following command from the command line or from PowerShell:
To upgrade SSL Certificate Verifier, run the following command from the command line or from PowerShell:
To uninstall SSL Certificate Verifier, run the following command from the command line or from PowerShell:
Deployment Method:
This applies to both open source and commercial editions of Chocolatey.
1. Enter Your Internal Repository Url
(this should look similar to https://community.chocolatey.org/api/v2/)
2. Setup Your Environment
1. Ensure you are set for organizational deployment
Please see the organizational deployment guide
2. Get the package into your environment
Option 1: Cached Package (Unreliable, Requires Internet - Same As Community)-
Open Source or Commercial:
- Proxy Repository - Create a proxy nuget repository on Nexus, Artifactory Pro, or a proxy Chocolatey repository on ProGet. Point your upstream to https://community.chocolatey.org/api/v2/. Packages cache on first access automatically. Make sure your choco clients are using your proxy repository as a source and NOT the default community repository. See source command for more information.
- You can also just download the package and push it to a repository Download
-
Open Source
-
Download the package:
Download - Follow manual internalization instructions
-
-
Package Internalizer (C4B)
-
Run: (additional options)
choco download sslverifier --internalize --source=https://community.chocolatey.org/api/v2/ -
For package and dependencies run:
choco push --source="'INTERNAL REPO URL'" - Automate package internalization
-
Run: (additional options)
3. Copy Your Script
choco upgrade sslverifier -y --source="'INTERNAL REPO URL'" [other options]See options you can pass to upgrade.
See best practices for scripting.
Add this to a PowerShell script or use a Batch script with tools and in places where you are calling directly to Chocolatey. If you are integrating, keep in mind enhanced exit codes.
If you do use a PowerShell script, use the following to ensure bad exit codes are shown as failures:
choco upgrade sslverifier -y --source="'INTERNAL REPO URL'"
$exitCode = $LASTEXITCODE
Write-Verbose "Exit code was $exitCode"
$validExitCodes = @(0, 1605, 1614, 1641, 3010)
if ($validExitCodes -contains $exitCode) {
Exit 0
}
Exit $exitCode
- name: Install sslverifier
win_chocolatey:
name: sslverifier
version: '1.5.7'
source: INTERNAL REPO URL
state: present
See docs at https://docs.ansible.com/ansible/latest/modules/win_chocolatey_module.html.
chocolatey_package 'sslverifier' do
action :install
source 'INTERNAL REPO URL'
version '1.5.7'
end
See docs at https://docs.chef.io/resource_chocolatey_package.html.
cChocoPackageInstaller sslverifier
{
Name = "sslverifier"
Version = "1.5.7"
Source = "INTERNAL REPO URL"
}
Requires cChoco DSC Resource. See docs at https://github.com/chocolatey/cChoco.
package { 'sslverifier':
ensure => '1.5.7',
provider => 'chocolatey',
source => 'INTERNAL REPO URL',
}
Requires Puppet Chocolatey Provider module. See docs at https://forge.puppet.com/puppetlabs/chocolatey.
4. If applicable - Chocolatey configuration/installation
See infrastructure management matrix for Chocolatey configuration elements and examples.
This package was approved as a trusted package on 20 Mar 2021.
Features
- Validates the SSL certificate and validates all certificates in the chain for possible errors;
- Implements certificate expiration checking. Certificate expiration is checked for all certificates in the chain;
- The tool also checks certificates for all possible redirection URLs;
- Writes trace/debug log for each processed entry;
- Provides an ability to save server list to a file and read the list from a file.
Main Window
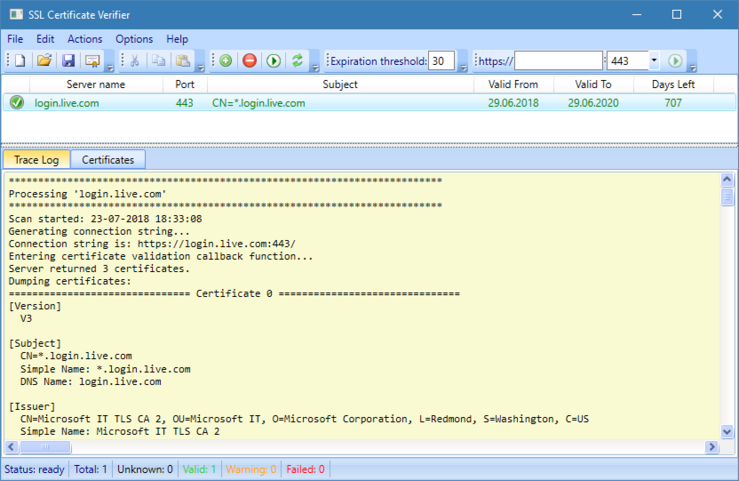
Main window contains a list of remote SSL/TLS servers and control buttons. There are three possible validation outcomes:
Ok
Client was able to successfully connect to remote server over SSL/TLS and its certificate passed all validation checks based on current settings.Error
Client was either, not able to connect to remote server over SSL/TLS or its certificate failed certificate validation checks.Warning
Client was able to successfully connect to remote server over SSL/TLS and its certificate passed all validation checks, but its certificate is about to expire:
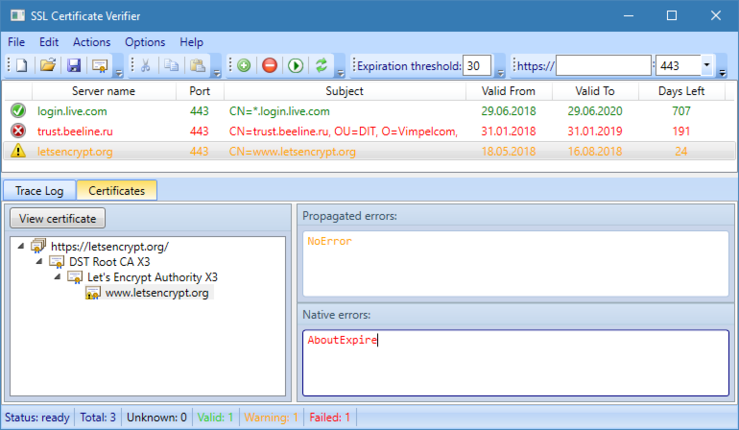
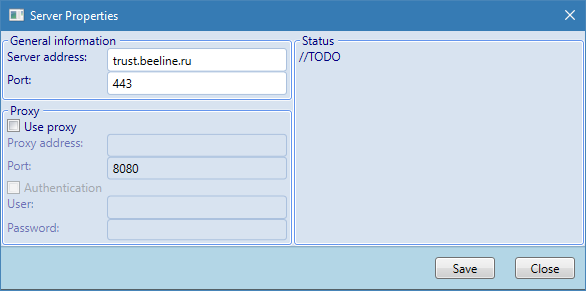
When selecting particular entry, a trace log with certificate details is shown. Right-click on remote server entry and selecting entry properties it is possible to configure proxy settings if necessary:
Certificate View
Additionally, there is certificate view which is located under Certificates tab:
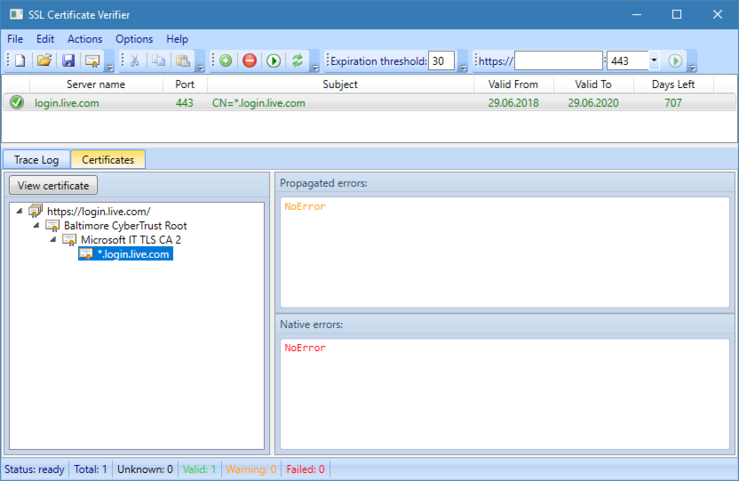
Certificate view dialog shows certificate chain and errors. Native errors shows potential issues with selected certificate itself. Propagated errors show potential issues propagated from upper level certificates (intermediate CA certificates). The following image shows errors associated with a certificate that failed validation checks:
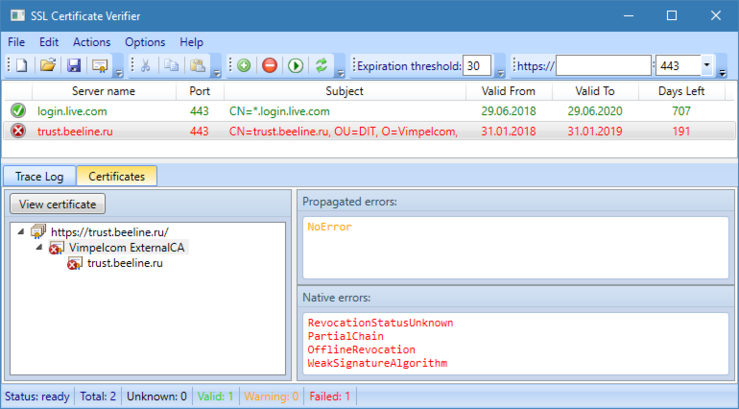
By pressing View Certificate button, a certificate UI dialog (provided by operating system) is shown.
Application Settings
Application contains several settings, which are invoked via Options -> Settings:
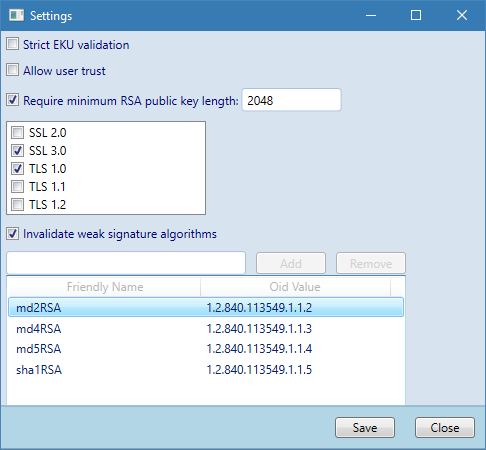
In this dialog, you can configure some validation options:
Strict EKU validation
When enabled, this option will require that entire certificate chain is valid for Server Authentication enhanced key usage. Otherwise, Server Authentication EKU is checked on leaf certificate only.Allow user trust
By default, certificate chains are built against trusted root CA store in machine context (local computer). Manually added trusted root CAs in current user store are not trusted by default.Require minimum RSA public key length
Enforces RSA public key length which must be equals or greater than specified value. This settings has effect only on RSA public keys. ECC (ellyptic curve cryptography) key length is not enforced.Protocol list
Specifies allowed SSL/TLS protocols. SSL Verifier Tool attempts to connect to remote server using the best protocol. If connection fails and there are other allowed protocols, they are attempted until connection succeeds or there are more allowed SSL/TLS protocols, otherwise, connection will fail.Invalidate weak signature algorithm
When enabled, specifies a set of disallowed signature algorithm for leaf and intermediate CA certificates. Signature algorithm list is not applied to root (presented in a self-signed form) are not checked.
From: https://raw.githubusercontent.com/Crypt32/SSLVerifier.WPF/master/LICENSE.md
LICENSE
# Microsoft Public License (Ms-PL)
Copyright (c) 2019 Vadims Podans
This license governs use of the accompanying software. If you use the software, you accept this license. If you do not accept the license, do not use the software.
1. Definitions
The terms "reproduce," "reproduction," "derivative works," and "distribution" have the same meaning here as under U.S. copyright law.
A "contribution" is the original software, or any additions or changes to the software.
A "contributor" is any person that distributes its contribution under this license.
"Licensed patents" are a contributor's patent claims that read directly on its contribution.
2. Grant of Rights
(A) Copyright Grant- Subject to the terms of this license, including the license conditions and limitations in section 3, each contributor grants you a non-exclusive, worldwide, royalty-free copyright license to reproduce its contribution, prepare derivative works of its contribution, and distribute its contribution or any derivative works that you create.
(B) Patent Grant- Subject to the terms of this license, including the license conditions and limitations in section 3, each contributor grants you a non-exclusive, worldwide, royalty-free license under its licensed patents to make, have made, use, sell, offer for sale, import, and/or otherwise dispose of its contribution in the software or derivative works of the contribution in the software.
3. Conditions and Limitations
(A) No Trademark License- This license does not grant you rights to use any contributors' name, logo, or trademarks.
(B) If you bring a patent claim against any contributor over patents that you claim are infringed by the software, your patent license from such contributor to the software ends automatically.
(C) If you distribute any portion of the software, you must retain all copyright, patent, trademark, and attribution notices that are present in the software.
(D) If you distribute any portion of the software in source code form, you may do so only under this license by including a complete copy of this license with your distribution. If you distribute any portion of the software in compiled or object code form, you may only do so under a license that complies with this license.
(E) The software is licensed "as-is." You bear the risk of using it. The contributors give no express warranties, guarantees or conditions. You may have additional consumer rights under your local laws which this license cannot change. To the extent permitted under your local laws, the contributors exclude the implied warranties of merchantability, fitness for a particular purpose and non-infringement.
VERIFICATION
Verification is intended to assist the Chocolatey moderators and community
in verifying that this package's contents are trustworthy.
Package can be verified like this:
1. Download:
x32: https://www.pkisolutions.com/download/16432/
x64: https://www.pkisolutions.com/download/16432/
2. You can use one of the following methods to obtain the SHA256 checksum:
- Use powershell function 'Get-FileHash'
- Use Chocolatey utility 'checksum.exe'
checksum type: sha256
checksum32: 7b86b5d22a2b699e7c6e79a0586d2f472ee91c37d99010f6b70c1580b20ef9a3
checksum64: 7b86b5d22a2b699e7c6e79a0586d2f472ee91c37d99010f6b70c1580b20ef9a3
File 'LICENSE.txt' is obtained from:
https://raw.githubusercontent.com/Crypt32/SSLVerifier.WPF/master/LICENSE.md
# Remove start menu shortcut
$programs = [environment]::GetFolderPath([environment+specialfolder]::Programs)
$shortcutFilePath = Join-Path $programs "SSLVerifier.lnk"
if (Test-Path $shortcutFilePath) { Remove-Item $shortcutFilePath }md5: 0E985C2322384814DDEE5B8861BA1B1D | sha1: B0E3F37E5187764615233C52FAE61D466BA79B04 | sha256: 7B86B5D22A2B699E7C6E79A0586D2F472EE91C37D99010F6B70C1580B20EF9A3 | sha512: DB98641FC297A574BECEAD6DC939601CE2F7E4BE4933A9952506F69360D4BD8F768D97F9F4A78AEDB7CBEE8B04CE09A6B23CD93CEAFCB98F6F01F3E51271DD6BLog in or click on link to see number of positives.
- sslverifier.1.5.7.nupkg (1c03bb2ece8f) - ## / 65
- SSL Verifier-v1.5.7.exe (7b86b5d22a2b) - ## / 69
In cases where actual malware is found, the packages are subject to removal. Software sometimes has false positives. Moderators do not necessarily validate the safety of the underlying software, only that a package retrieves software from the official distribution point and/or validate embedded software against official distribution point (where distribution rights allow redistribution).
Chocolatey Pro provides runtime protection from possible malware.
| Add to Builder | Version | Downloads | Last Updated | Status |
|---|---|---|---|---|
| SSL Certificate Verifier 1.5.7 | 694 | Saturday, March 20, 2021 | Approved | |
| SSL Certificate Verifier 1.5.6.1 | 126 | Sunday, February 21, 2021 | Approved | |
| SSL Certificate Verifier 1.5.5 | 130 | Friday, February 5, 2021 | Approved | |
| SSL Certificate Verifier 1.5.4 | 244 | Tuesday, August 11, 2020 | Approved | |
| SSL Certificate Verifier 1.3.0.1 | 478 | Monday, September 9, 2019 | Approved | |
| SSL Certificate Verifier 1.3 | 227 | Saturday, May 4, 2019 | Approved |
© 2008 - 2019 - Sysadmins LV. All rights reserved
This package has no dependencies.
Ground Rules:
- This discussion is only about SSL Certificate Verifier and the SSL Certificate Verifier package. If you have feedback for Chocolatey, please contact the Google Group.
- This discussion will carry over multiple versions. If you have a comment about a particular version, please note that in your comments.
- The maintainers of this Chocolatey Package will be notified about new comments that are posted to this Disqus thread, however, it is NOT a guarantee that you will get a response. If you do not hear back from the maintainers after posting a message below, please follow up by using the link on the left side of this page or follow this link to contact maintainers. If you still hear nothing back, please follow the package triage process.
- Tell us what you love about the package or SSL Certificate Verifier, or tell us what needs improvement.
- Share your experiences with the package, or extra configuration or gotchas that you've found.
- If you use a url, the comment will be flagged for moderation until you've been whitelisted. Disqus moderated comments are approved on a weekly schedule if not sooner. It could take between 1-5 days for your comment to show up.









 Ansible
Ansible

 PS DSC
PS DSC
